ABSTRACT
As the Internet of Things (IoT) has developed, the emerging sensor network (ESN) that integrates emerging technologies, such as autonomous driving, cyber-physical systems, mobile nodes, and existing sensor networks has been in the limelight. Smart homes have been researched and developed by various companies and organizations. Emerging sensor networks have some issues of providing secure service according to a new environment, such as a smart home, and the problems of low power and low-computing capacity for the sensor that previous sensor networks were equipped with.
This study classifies various sensors used in smart homes into three classes and contains the hierarchical topology for efficient communication. In addition, a scheme for establishing secure communication among sensors based on physical unclonable functions (PUFs) that cannot be physically cloned is suggested in regard to the sensor’s low performance. In addition, we analyzed this scheme by conducting security and performance evaluations proving to constitute secure channels while consuming fewer resources. We believe that our scheme can provide secure communication by using fewer resources in a smart home environment in the future.
RELATED WORKS
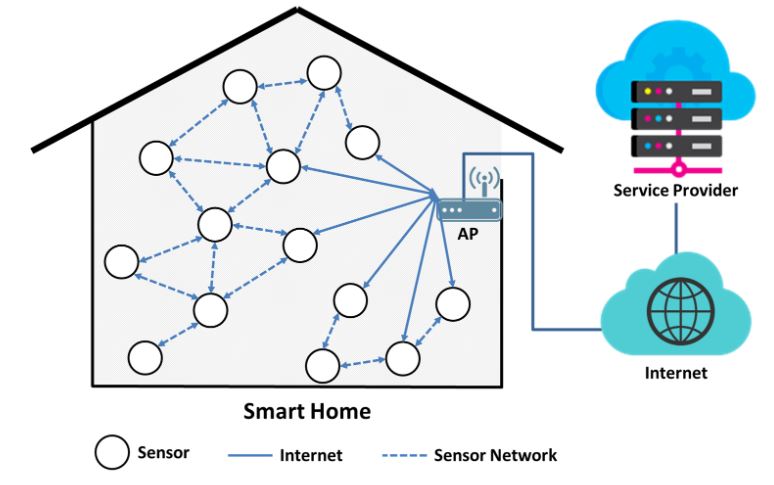
Figure 1. Existing topology in a smart home sensor network
Figure 1 shows the infrastructure of a typical smart home. Various sensors in the smart home communicate with each other through a sensor network to provide service to, and collect information from, residents. Each of the sensors exchanges information with the service provider through the AP and if a sensor cannot directly reach the AP, it communicates through the other sensors.
A smart home sensor network requires a topology for securely and efficiently exchanging information in regards to computing ability and the power capacity of various sensors. However, most of the suggested sensor networks propose various topologies or infrastructures that lack a diversity in sensor ability. Therefore, it is inappropriate to apply them to an actual smart home sensor network.
PROPOSED INFRASTRUCTURE
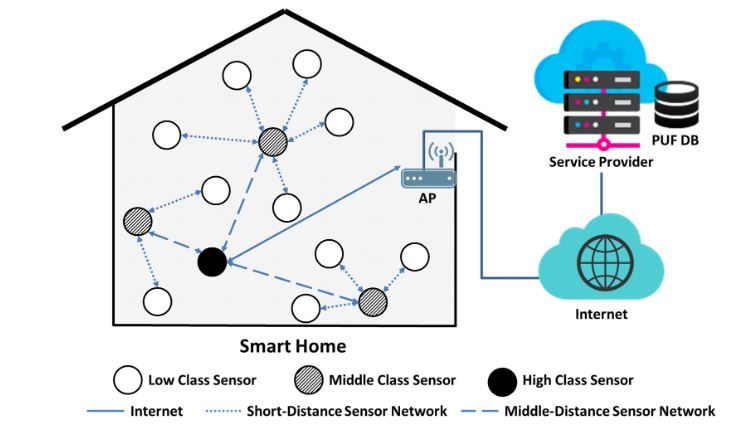
Figure 2. Proposed hierarchical topology in a smart home sensor network
Figure 2 shows the hierarchical topology that is suggested in this paper in consideration of the capabilities of various sensors in a smart home environment. Sensor networks in the smart home have been classified into three classes of low, middle, and high-class from sensors with low resources to ones with high resources for the capabilities of each sensor. Low-class sensors are the smallest and most affordable. Therefore, they are distributed the most in the smart home. Middle-class sensors are not distributed as widely as low-class sensors.
SECURITY AND PERFORMANCE ANALYSIS
Suggested techniques have classified each of the sensors into three classes depending on the capabilities of computing ability and battery life, while constituting a hierarchical topology and performing the mutual authentication and key agreement phases amongst sensors and between the sensor and service provider. In addition, our suggested techniques are secure against keys being leaked, forward secrecy, eavesdropping, and replay attacks by malicious attackers, and they are highly secure and efficient compared to other methods. Therefore, they support the row resource sensor environment.
CONCLUSIONS
A smart home is a form of technology that can collect and analyze the information of those who reside there by using various sensors and emerging technologies. Emerging technologies have been combined with IoT, which has resulted in creating smart home service as a new field of ESNs. As such, various companies and research institutions around the world have been proceeding with research and development. Most of the sensors in this service are equipped with low-power and low-computing ability.
Therefore, it is very important to deliver sensing information without placing a burden on the sensor, which is why topology control is required. In this study, sensors with low resources and sensors with diverse capabilities operating in the smart home were considered and classified into low, middle, and high-class, depending on their ability to constitute the hierarchical topology. Therefore, in this study, we have proposed a technique for ensuring secure communication, and consuming low computing and storage resources with PUF while efficiently utilizing the abilities of the sensors.
In addition, our technique has been evaluated to be secure against various security threats via the execution of a security analysis. Our proposed scheme was also evaluated by analyzing the computing resources and storage resources needed by each communicator. However, there are still some problems, such as multi-platform compatibility and security policies set according to the importance of information, that we will study in the future. We believe that our scheme will be able to establish secure communication with fewer resources in the smart home sensor network.
Source: Soongsil University
Authors: Mansik Kim | Kyung-soo Lim | Jungsuk Song | Moon-seog Jun